Five Facts Unveiled by the National Police's Criminal Investigation Unit Regarding the Fake E-Ticket Case Controlled by Chinese Nationals
The Directorate of Cyber Crime (Dittipidsiber) of the National Police’s Criminal Investigation Unit (Bareskrim) has uncovered a phishing SMS blast case that mimics the official e-ticket website. The case of the fake e-ticket was directly controlled by Chinese nationals.
Based on detikcom’s records, Thursday (February 26, 2026), this case was revealed after a report was submitted by the Attorney General’s Office (Kejagung) in December 2025 regarding the circulation of several fake links that impersonated government institutions. The police then took action to follow up on the case.
The disclosure of this case was also previously conveyed by the National Police Chief, General Listyo Sigit Prabowo, in a working meeting at Commission III of the Indonesian House of Representatives (DPR RI), in the parliamentary complex, Senayan, Jakarta, last Monday (January 26).
The National Police Chief stated that there were already suspects in this case.
“One of the prominent cybercrimes is the handling of the SMS blast phishing case with the e-ticket modus operandi,” said the National Police Chief.
The National Police Chief said that the initial disclosure of this case came from a report received by the police. Initially, the police found 11 phishing links and 5 international format telephone numbers used for the cybercrime. From this report, similar cases were then found in the Central Sulawesi Police.
SMS messages containing phishing links will direct victims to a fake e-ticket website. The victims then fall victim to fraud.
Here are the facts about the fake e-ticket case after it was revealed:
Fake E-Tickets Controlled by Chinese Nationals
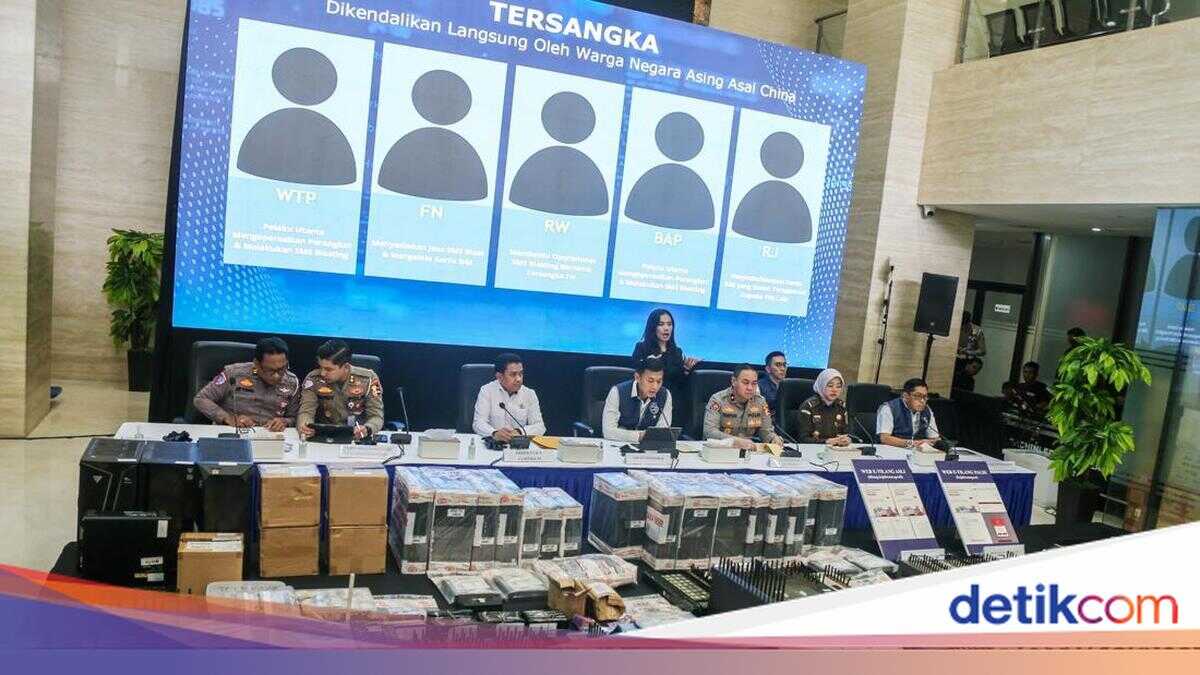
The Directorate of Cyber Crime (Dittipidsiber) of the National Police’s Criminal Investigation Unit (Bareskrim) then arrested five suspects in the online fraud or phishing case with the SMS blast modus operandi for fake e-ticket payments. The Head of Dittipidsiber of the National Police’s Criminal Investigation Unit, Brigadier General Himawan Bayu Aji, said that the crime was controlled by Chinese nationals.
“Investigators conducted further investigation and examination of the five suspects and found that this crime was directly controlled by foreign nationals from China,” said Himawan in a press conference at the National Police’s Criminal Investigation Unit, South Jakarta, Wednesday (February 25).
Himawan said that the suspects in Indonesia were accomplices who received and carried out orders from Chinese nationals using the Telegram accounts Lee SK and Daisy Qiu.
“In supporting its operations in Indonesia, the perpetrators from China sent SIM boxes (devices used for blasting) directly to the suspects in Indonesia,” explained Himawan.
Himawan said that the Chinese nationals controlled the perpetrators in Indonesia to install SIM cards into SIM boxes or modem pools. The system is controlled remotely or automatically from China.
The suspects in Indonesia then only opened the Terminal Vendor System or TVS application. Through this application, the suspects allegedly monitored the number of SMS blasts sent and failed.
“In one day, the SIM box devices operated by the suspects were able to send phishing SMS messages to 3,000 mobile phone numbers. To operate the SIM boxes sent from China, the perpetrators needed hundreds of SIM cards that had been registered using the NIK (National Identity Number) and data of Indonesian citizens,” he said.
5 Suspects Arrested
The Directorate of Cyber Crime (Dittipidsiber) of the National Police’s Criminal Investigation Unit (Bareskrim) revealed that the five suspects who had been arrested were WTP (29), FN (41), RW (40), BAP (38), and RJ (29). They each had different roles.
Here are the roles of the five suspects in Indonesia:
WTP, who played the role of the main perpetrator who operated the devices and carried out SMS blasting since September 2025.
FN, who played the role of providing SMS blast services with clients who were foreign nationals, and also managed SIM cards since July 2025.
RW, who played the role of assisting in the operational SMS blasting with suspect FN since July 2025.
BAP, who played the role of the main perpetrator of SMS blasting and operator of the blasting device since February 2025.
RJ, who played the role of providing or selling SIM cards that had been registered to other perpetrators.
Chinese Nationals, Suppliers of Blasting Devices, Being Hunted
The police are not stopping there and are continuing to investigate the case. Currently, the police are hunting for two Chinese nationals who control the online fraud syndicate with the SMS blast modus operandi for fake e-ticket payments.
“For these two Chinese controllers, we are currently investigating and we have obtained their identities, coordinating with the International Relations Division and Interpol,” said Brigadier General Himawan.
The two Chinese nationals used Telegram accounts with the names Lee SK and Daisy Qiu to communicate with the five suspects. Himawan said that they would soon issue a red notice for both of them.
“We will issue a red notice and we are also in intensive communication with China, because the sender’s address is listed there. We will ensure whether the address is indeed there or a fake address for the two of them,” he explained.
The Chinese nationals had visited Indonesia and met face-to-face with the suspects. The Chinese nationals also taught them how to operate the SIM box devices used for SMS blasts.
“The perpetrators from China sent SIM boxes, devices used for blasting, directly to the suspects in Indonesia,” said Himawan.
“Of the 7 SIM box units, two shipments in September and December 2025 could be identified, and the rest are still being investigated by investigators,” he added.
Operators Paid in Crypto Up to IDR 1 Billion
Brigadier General Himawan then explained in detail the role of the operators of the SMS blasting devices. He said that the suspects reaped profits through cryptocurrency (USDT).
“The suspects received monthly salaries in the form of cryptocurrency or USDT. Starting from 1,500 USDT or around IDR 25 million to 4,000 USDT or around IDR 67 million, depending on the number of SIM boxes operated,” said Himawan.
Himawan detailed that one of the suspects, with the initials BAP (38), was recorded as the largest recipient of profits, namely almost IDR 1 billion.
“BAP received a total of 53,000 USDT or around IDR 890 million in 142 transactions from February 2025 to January 2026,” said Himawan.
Appeal to the Public Not to Easily Believe SMS Messages with Links
Furthermore, Brigadier General Himawan then gave an appeal to the public regarding
