Fake E-Fine Scam: Operators Paid in Cryptocurrency
Police have successfully uncovered an online fraud or phishing case involving fake e-fine payment SMS messages. The suspects in this case were paid in cryptocurrency.
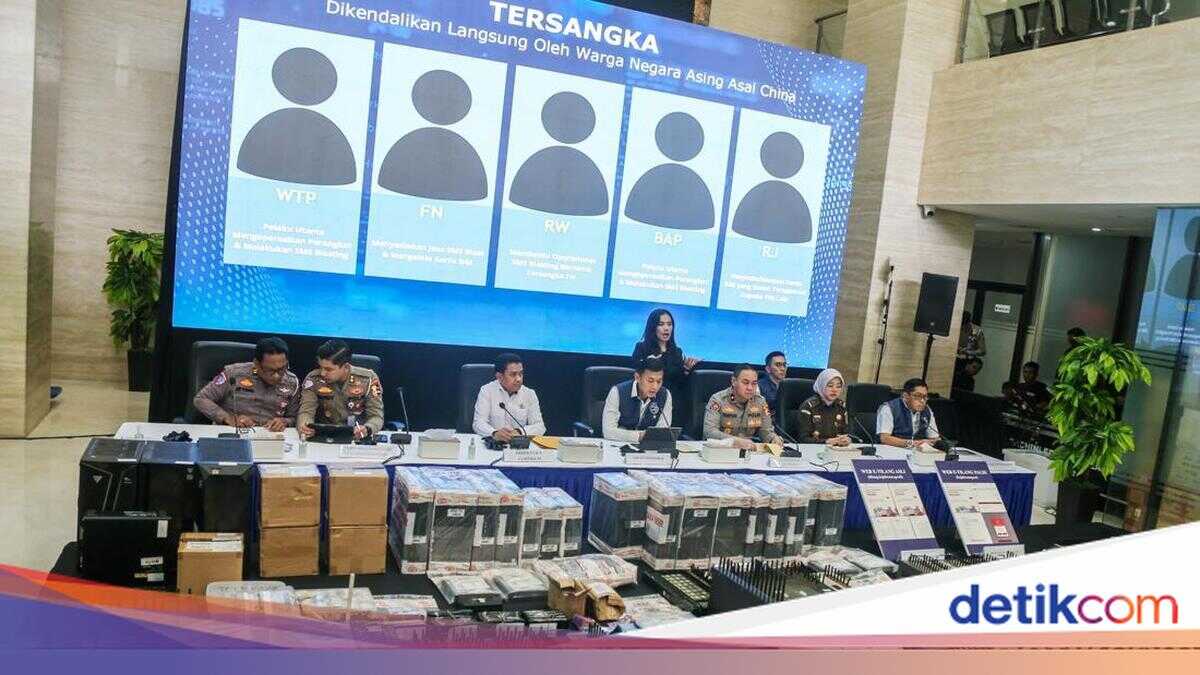
The Directorate of Special Cyber Crimes (Dittipidsiber) of the National Police’s Criminal Investigation Unit (Bareskrim) has arrested five suspects in this case. The Head of Dittipidsiber Bareskrim Polri, Brigadier General Himawan Bayu Aji, said that the five suspects are WTP (29), FN (41), RW (40), BAP (38), and RJ (29). They each had a role in the case.
“Investigators conducted further investigation and examination of the five suspects and found that this crime was directly controlled by a foreign national from China,” said Himawan in a press conference at Bareskrim Polri, South Jakarta, Wednesday (25/2/2026).
Himawan said that the suspects in Indonesia were accomplices who received and carried out orders from Chinese nationals using the Telegram accounts Lee SK and Daisy Qiu.
“In supporting their operations in Indonesia, the perpetrators from China sent SIM boxes (devices used for blasting) directly to the suspects in Indonesia,” explained Himawan.
Here are the roles of the five suspects in Indonesia:
WTP, who acted as the main perpetrator operating the device and carrying out SMS blasting since September 2025.
FN, who provided SMS blast services with foreign national clients and managed SIM cards since July 2025.
RW, who helped with the SMS blasting operations with suspect FN since July 2025.
BAP, who acted as the main perpetrator of SMS blasting and operator of the blasting device since February 2025.
RJ, who acted as the provider or seller of registered SIM cards to other perpetrators.
Controlled by Chinese Nationals
Himawan said that the Chinese nationals controlled the perpetrators in Indonesia to install SIM cards into SIM boxes or modem pools. The system was controlled remotely or automatically from China.
The suspects in Indonesia then opened the Terminal Vendor System or TVS application. Through this application, the suspects allegedly monitored the number of SMS blasts sent and failed.
“In one day, the SIM box devices operated by the suspects were able to send phishing SMS messages to 3,000 mobile phone numbers. To operate the SIM boxes sent from China, the perpetrators needed hundreds of SIM cards that had been registered using the NIK (National Identity Number) and data of Indonesian citizens,” he said.
Chronology of the Fraud
The incident began when the victim received an SMS from an unknown number. The SMS informed the victim of outstanding traffic violation fines and included a link.
“Then the victim clicked on the link and was directed to a fake e-fine website that looked very similar to the official website of the Prosecutor’s Office,” explained Himawan.
Believing that the website was genuine, the victim entered their personal data and credit card information. This resulted in an illegal debit transaction on the victim’s credit card for 2,000 Saudi Arabian riyals, equivalent to Rp 8.8 million.
In response, the police conducted an investigation and found 124 other phishing website links. In addition, the police also found six additional mobile phone numbers used by the perpetrators to spread SMS blasts.
Paid in Cryptocurrency
The suspects received monthly salaries in the form of cryptocurrency or USDT as compensation, ranging from 1,500 USDT or around Rp 25 million to 4,000 USDT or around Rp 67 million, depending on the number of SIM boxes operated.
“The suspects received monthly salaries in the form of cryptocurrency or USDT, ranging from 1,500 USDT or around Rp 25 million to 4,000 USDT or around Rp 67 million, depending on the number of SIM boxes operated,” said Himawan.
Himawan detailed that one of the suspects, with the initials BAP (38), was the largest recipient of profits, amounting to almost Rp 1 billion.
“BAP received a total of 53,000 USDT or around Rp 890 million in 142 transactions from February 2025 to January 2026,” said Himawan.
Then, suspect RW received a total of 42,300 USDT or around Rp 700 million from June 2025 to January 2026. Suspect FN received a total of 14,100 USDT or around Rp 235 million from July 2025 to January 2026.
Then, WTP received a total of 32,700 USDT or around Rp 530 million in 43 transactions from September 2025 to January 2026.
“The profits or commissions were regularly exchanged for Rupiah currency each month by the suspects,” said the investigator in Himawan’s statement.
For their actions, the five suspects were charged with Article 51 in conjunction with Article 35 of Law Number 1 of 2024 concerning the Second Amendment to Law Number 11 of 2008 concerning Information and Electronic Transactions. And/or Article 45A paragraph 1 in conjunction with Article 28 paragraph 1 of Law Number 1 of 2024 concerning the Second Amendment to Law Number 11 of 2008 concerning Information and Electronic Transactions and/or Article 3, 4, 5, and 10 of Law Number 8 of 2010 concerning Money Laundering. And/or Article 607 paragraph 1 letters a, b, and c of Law Number 1 of 2023 concerning the Criminal Code in conjunction with Article 20 letter c of Law Number 1 of 2023 concerning the Criminal Code.
“With a maximum prison sentence of 15 years and a maximum fine of Rp 12 billion,” he said.
