2.8 Billion Passwords in Hackers' Hands: Switch to This Immediately
Jakarta, CNBC Indonesia - Cybercrime threats are increasingly alarming. The latest data reveals a significant surge in ransomware victims throughout 2025.
The State of Cybercrime 2026 report from KELA records a 45% annual increase in ransomware victims. At the same time, 2.86 billion credentials, ranging from passwords to cookies, are known to have leaked and are being traded on the dark web.
Even more shocking, over 30% of the exposed data comes from business cloud services and authentication systems.
Not only that, the trend of malware infections has also risen sharply. KELA notes that infostealer malware infections on macOS devices surged dramatically from under 1,000 cases in 2024 to over 70,000 cases in 2025, an increase of up to 7,000%.
“Infostealer malware is designed to extract sensitive data from infected devices, including login credentials, authentication tokens, and other important account information,” the report states, quoted from Forbes, on Monday (4/5/2026).
Throughout 2025, around 3.9 million devices worldwide were infected with this type of malware, resulting in over 347 million credentials successfully stolen.
Attack methods are becoming increasingly sophisticated. From AI-based scams, paid phishing (phishing-as-a-service), to malware distribution via advertisements and fake search results. Users are also often tricked into “hacking” their own devices by running malicious scripts unknowingly.
On the other hand, law enforcement operations by the FBI have not been able to stem the tide of these threats. The malware-as-a-service business model has instead made cybercriminals even easier to carry out their actions.
Given this situation, security experts emphasise the importance of layered protection. Users are urged to regularly update systems, avoid suspicious links, and use password managers.
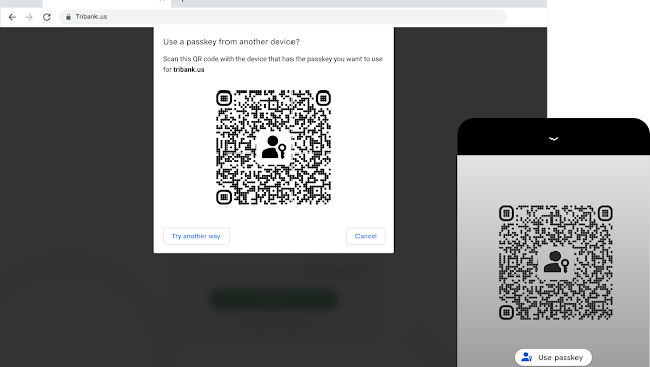
In addition, enabling two-factor authentication (2FA) is also considered crucial. However, with the growing prevalence of 2FA bypass techniques through session cookie theft, users are advised to switch to passkey technology.
Unlike passwords, passkeys are stronger, cannot be stolen via phishing or intercepted during transmission. This technology stores the private key directly on the user’s device, making it nearly impossible to hack through interception or infostealer malware as mentioned in this report.
